Learn how blockchain truly works, master key definitions, and uncover what makes smart contracts so "smart." Dive into the fundamentals, gain valuable insights, and start your blockchain journey today!

- Blockchain
Hasib Anwar
- on July 30, 2021
Blockchain Technology Explained: A Decentralized Ecosystem
Blockchain technology is more or less, slowly taking over the digital world. One thing I can say for sure is that this tech is going to disrupt almost all of the industries on the market now. So, now is the time to get to know everything there is to know about it.
Surely the blockchain is a sophisticated technology, and there are many elements within the core system that needs explaining. In reality, all of these can be quite overwhelming for a beginner.
That’s why in this blockchain technology explained guide, I will explain all the properties and features of blockchain that makes it so distinctive.
So, I hope you’ll thoroughly enjoy this. Let’s start explaining!
Build your identity as a certified blockchain expert with 101 Blockchains’ Blockchain Certifications designed to provide enhanced career prospects.
Table of Contents
Chapter-1: What Is Blockchain Technology?
Chapter-2: Layers of Blockchain Technology
Chapter-3: What Are Smart Contracts?
Chapter-4: Different Consensus Algorithms
Chapter-5: Web3: The New Internet
Chapter-6: Examples of Enterprise Blockchains
Chapter-7: Concluding Thoughts
Chapter-1: What Is Blockchain Technology?
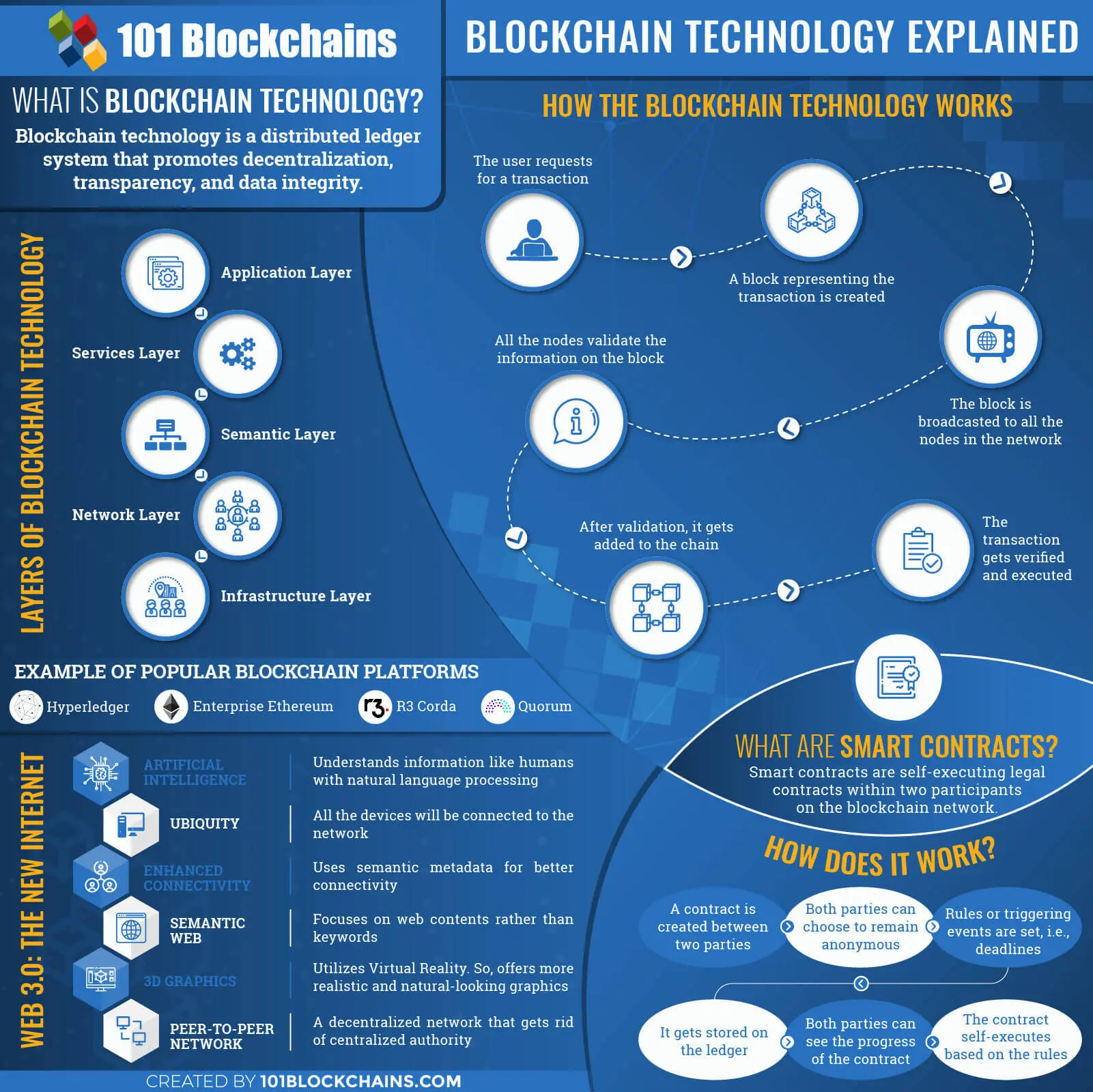
Let’s start with the most basic question of all time – “What is definition of blockchain technology?” Well, blockchain technology is a distributed ledger system that promotes decentralization, transparency, and data integrity.
Please include attribution to 101blockchains.com with this graphic. <a href='https://101blockchains.com/blockchain-infographics/'> <img src='https://101blockchains.com/wp-content/uploads/2019/07/Blockchain-technology-explained.jpg' alt='Blockchain technology explained='0' /> </a>
Does it seem confusing?
Let me explain blockchain technology in a simple way. Imagine multiple blocks that are connected in a chain-like a format. Here, all the blocks will be linked to the previous block and the block in front of it.
Moreover, all the blocks in that chain contain some form of data, and the chain represents the linking structure. In reality, every single block will link using the cryptography. Moreover, all the blocks in that chain will have a cryptographic hash ID along with transactional data and timestamps.
And so you end with a growing chain of blocks, and that is my friend what a blockchain is. You could think of it as a database that stores information in a unique way. But blockchain and databases are practically quite different in nature even though they both store information.
By default, blockchain technology does not support any modification of the data. So, any data that would go in the block can never get deleted or altered. Thus, it will stay there forever. Another significant fact about blockchain technology explained is that the network is a peer-to-peer network.
So, there is no centralized connection lurking in the shadows trying to steal your information. I mean, who wouldn’t like this much freedom, right?
Blockchain Technology Explained: How Does It Work?
Well, it’s time for you to know how the tech actually works in this blockchain guide. But before we begin, take a look at some of the important features to know about beforehand.
Blockchain stored all the information in a ledger system. Moreover, any kind of data exchanges is called “transactions.” Previously blockchain was only meant for transacting digital currencies, but now it can even use other forms of data as well.
Every single user on the network is called “nodes,” and they get a copy of the updated ledger. Moreover, every node has a different way of communicating with each other. The system varies from blockchain to blockchain.
Now let’s begin the explanation of blockchain technology!
First of all, a user will request for a transaction in the network. Here, he/she will get two keys – public and private. But the user can only transact using the private key. And to find the other person you are sending money to you will need their public key.
Anyhow, after the request a block with all the information of the transaction gets created. In reality, everything in the block is encrypted to promote security.
Once it’s created, it will be broadcasted to all the nodes in the network. In blockchain technology explained you need verification from other nodes that what you claimed is valid. And so the other nodes use a consensus algorithm (I’ll explain what it is a bit later) to validate the information.
Once your block gets validated, the block will get a spot on the chain. At the same time, the transaction you did will be executed as well.
Understanding how it works doesn’t seem that much difficult now, does it?
Check Out Our Blockchain Vs. Database Guide To Know The Difference Between These Two.
Chapter-2: Layers of Blockchain Technology
Now let’s talk about the different layers of the blockchain technology in this explanation of blockchain guide. Primarily there are 5 different layers of the tech, and we’ll get to every single one of them here.
So, let’s start.
1. Application Layer
At first, let’s talk about the application layer. In reality, it comes with dApps, dApp browser, User interface, and the application hosting.
Using the dApp browser, you can get access to the decentralized applications. Unfortunately, typical browsers like Chrome or Firefox isn’t capable of browsing through decentralized applications. So, in this one, you will get a completely different user interface similar to typical browsers.
However, with these, you can also surf the regular internet.
Next, the application hosting lets you run all the decentralized application in this layer. Without this element, no dApps can be live on the internet. Obviously, the hosting protocol will be fully decentralized as well. Moreover, maintaining these hosting servers are absolutely secure as they have a low risk.
Next comes the decentralized applications. Typically these are similar to today’s application but with one distinct change. All of them have a decentralized network. Furthermore, these are extremely easy to make nowadays.
Must Check: Beginner’s Guide To DApp Development
2. Services Layer
This is the second layer after the application layer. In this one, you’ll get access to all the essential tools that will help you build and run the dApps layer. In reality, in this blockchain explained layer, it covers all the vital elements.
More so, you’ll get your hands on governance, off-chain computing, state channels, data feeds, and side chains.
Data feeds are a process that helps to get the most updated information from all the credible sources. So, it will help the nodes to get the latest updates information about the network.
On the other hand, off-chain computing is here to get the computing process done outside the blockchain. Furthermore, it promotes additional privacy and takes the burned off the core network system.
Additionally, you’ll get a governance structure here as well. In reality, these are basically a human-less autonomous organization that can promote a fair environment.
Furthermore, the state channel actual is the pathway between two nodes. So, using state channels, two nodes can communicate with each other.
Other than these, there are also other elements in blockchain explained layers. Mainly these are Oracles, Multi-signatures, Smart contracts, Digital Assets, Wallets, Distributed file storages, Digital identities, etc.
These are optional because a blockchain technology may have it or not.
Oracles:
Oracles are necessary for smart contracts because they act as an agent for collecting information from outside the network.
Multi-signatures:
This element ensures a different kind of security protocol. In reality, you would need to sign any transaction without a unique signature for making a transaction. And here, you can choose how many of these signatures you want for transacting.
Smart contracts:
These are mainly self-executing legal contracts within two participants on the blockchain technology network. In reality, the whole system gets rid of the trust issue and lets you quickly exchange any kind of asset.
But we will get to it later in the blockchain guide.
Digital Assets:
Now on the blockchain technology stack, the digital asset can refer to anything. In reality, it can mean cryptocurrencies, shares, gold, or even other kinds of document. Furthermore, any digital element with real values in the real world would be known as digital assets.
Wallets:
Here, in the blockchain technology wallets are to store all the digital assets you will have on the network.
Distributed file storage:
In the explanation of blockchain technology, I can safely say that distributed file storages are actually a server location where all the data will be stored. Obviously, you’ll need authentication for accessing them.
Digital Identity:
In reality, Digital Identities are the identities of the users on the network. Furthermore, you will need it to have proper authentication on the network.
Let’s move on to the next layer in this blockchain explained guide.
3. Semantic Layer
In this layer, there are consensus algorithms, virtual machines, any kind of participation requirements, and so on.
There’s no blockchain network without consensus algorithms. In reality, consensus algorithms are absolutely necessary for maintaining an agreement between all the nodes. Practically, it’s a process where all the nodes come to the same agreement over the information on the ledger.
Furthermore, in the ledger, no one can just start a transaction and get it added. He/she may not be honest as well. So, to make sure that the information on the block is valid, all the nodes come to the same agreement. But we’ll talk more about it later in the blockchain explained guide.
Next comes the participation requirements. In reality, these are mainly rules that helps the network decide who can join the system and who can’t. Moreover, this element is basically for the private blockchain technologies out there.
On the other hand, virtual machines offer security and execution environment for all the tasks on the network.
Mostly, it’s used in the smart contract execution. Next comes the side chains where developers can go to another separated blockchain environment to develop decentralized applications without affecting the core network.
Anyhow, let’s move on to the next layer in the explanation of blockchain technology guide.
4. Network Layer
Another layer after the semantic is the network layer. It contains Trusted Execution Environment (TEE), Roll your own mechanism, RLPx, Block delivery network, and many more.
Basically trusted execution environment helps the architecture to maintain scalability issues. Not only it helps the network overcome this issue, but it also makes it more secure. Furthermore, it helps to store data away from the main network to take some of the loads off it.
Usually, these protocols are for when a standard protocol doesn’t fully adjust to the infrastructure. So, it lets you customize other protocols to better adapt to it. It’s best to work with standard ones. But in some cases, the standard might not be enough.
On the other hand, RLPx is a network suite that helps in the transportation of data between two peers. Anyhow, it creates an interface to help the users communicate in the blockchain network.
Lastly block delivery networks is a network system that will deliver a web content or page to you if you request for it. In reality, you can see it in the typical internet architecture.
But if you are working on a decentralized application you will need some kind of delivery system to access web content, won’t you?
Now let’s move on to the next layer in this explanation of blockchain technology.
Not sure how to build your career in enterprise blockchains? Enroll Now: How to Build Your Career in Enterprise Blockchains
5. Infrastructure Layer
This is the last layer in the blockchain technology architecture. In this one, you might come across mining as a service protocol. However, now, mining is slowly going away because of the excess power it needs.
On the other hand, virtualization is the means of creating any kind of virtual resources such as servers, network, storage, OS, etc. Furthermore, it operates in three levels – hardware, system, and server. Nodes are also a part of this layer. Any device connected to the network is considered a node.
In reality, without any nodes practically, there won’t be any blockchain technology at all. Another cool element of this layer is the decentralized storage of the network. As it’s decentralized, it’s more secure than ever.
In reality, you might see token on this layer as well. Tokens help maintain the ecosystem and are a native asset on the network.
So, these are the five layers of blockchain technology. Now let’s move on the next phase of this explain blockchain technology guide.
Chapter-3: What Are Smart Contracts?
Now let’s talk about one of the significant features of the blockchain technology in this explain blockchain technology guide. Previously you got a little bit of introduction to the smart contracts. But now we’ll dive into a bit deeper into this topic.
The usual definition would be –
Smart contracts are self-executing legal contracts within two participants on the blockchain network.
Typically with the smart contract, you can practically exchange any kind of asset such as money, property, shares, anything that is deemed valuable. Moreover, it lets you do it securely and transparently. Furthermore, in smart contracts, there’s no need for any intermediary.
Now there are many blockchain applications that come with smart contracts integration.
Thus, this is the main difference between the typical contracts. In case of any legal contracts, you would need to pay for the service and then get that in return.
However, here you won’t have to wait for the service to get done after paying for it. So, there’s no issue with trust at all. So, it’s kind of like a vending machine, where you can get candy or snacks right after the paying.
To help you better understand what the situation is, I’ll explain how it actually works in this explain blockchain technology guide.
How Does It Work?
First of all, a party creates a contract after the full agreement from two or more parties. When the contract is created, all the parties can choose to remain anonymous. In the typical private network space, mainly you would have to have a proper authentication process to enter the system.
So, when someone starts a smart contract with you, they will most probably know your identification as well. Well, at least you’d have to let them know about the public address.
After that, the parties would set any kind of rules that needs to be fulfilled in order for the contract to be valid. It could be anything or any triggering event. So, when that condition would be made, it’ll automatically trigger the next event.
Once everything gets set up, it’ll get verified and stored on the ledger. After that, everyone connected to that contract would be able to see the progress right from the network. Moreover, in case of tracking everything will be in real-time.
After fulfilling all the conditions to fulfill the contract, it’ll self-execute and distribute the money.
Basically, it’s a great way to automate the process of ay contract. As everything is automated and tracked right from the UI, it saves a lot of money and time.
Why Is Smart Contract So Beneficial?
Another important fact I should explain in this explain blockchain technology guide is that smart contracts highly beneficial. But why? Well, let’s find out.
- No Interruption: Due to getting rid of the middleman, there’s no annoying interruption time in the process.
- High Security: You can see everything right from the blockchain applications UI, so there’s no way anyone can scam you as you can just what the process is. Also, no one can hack the data on the smart contract to alter the outcome.
- Quite Fast: Typically processing everything manually takes up a lot of time. But when it’s on the blockchain applications network, it’ll flow quite fast.
- No human Error: Practically in many contracts, the human-made error cost a lot of money and time. But with this blockchain applications digital contract, the chance for that is entirely low.
- More Profit: In reality, getting rid of the intermediary gets rid of the extra payment option as well. So, that means more profit for you.
So, these are the advantages of smart contracts. Let’s move on the next phase of these basics of blockchain technology guide.
Chapter-4: Different Consensus Algorithms
-
Proof of Work
Proof of Work is the first-ever consensus algorithm in the blockchain network. As you know, bitcoin had the first working blockchain network, and it used proof of work. After that, many other blockchain networks use this method until now.
However, proof of work consumes a lot of power and is relatively slow. In this one, miner tends to solve complex mathematical problems using their devices computational power. Basically, it’s for verifying every single block on the chain.
Let’s move on to the next algorithms in the basics of blockchain technology guide.
-
Delayed Proof of Work
This is another version of the proof of work algorithm. You could think of it as a hybrid model. In reality, this one allows the network to take advantage of the power of hashing from another blockchain network.
But how? Well, some notary nodes add data from the first blockchain to the second one, thus securing the power. Any blockchain network working on the dPoW can use either PoS or PoW to function properly. Anyhow, this one is much faster than the original proof of work.
-
Proof of Stake
Proof of stake actually came because of the limitations of the proof of work. Here, every single block will be validated before any other block comes along. Moreover, the miners here can stake their coins and take part in the process.
But here the taking participation would depend mostly on the possession of coins. So, if you have a minimum amount of coin, you can take part or else you can’t. In reality, proof of stake is much faster and less power consuming than PoW.
-
Delegated Proof of Stake
This is another variation of the proof of stake algorithm. In reality, this one is much more robust and flexible than other algorithms so far. Furthermore, all the nodes here are delegates. There’s also a concept of witnesses that are selected through voting. After they validate each node, they get paid accordingly. Also, the delegates are chosen using voting as well. And mainly these nodes are responsible for changing the parameters of the system.
However, they do not get paid the same as the witnesses. Anyhow, let’s move on to the next one in the basics of blockchain technology guide.
-
Leased Proof of Stake
Leased proof of stake is yet another entry in the basics of blockchain technology. In reality, the Waves uses this consensus algorithm. Furthermore, the process limits the use of power in any way possible.
Here, smallholders can lease their coin to the network and take part in the consensus process. So, there’s no issue of unfair rules in this one. As the small coin holders never got a chance in the previous PoS algorithms, here, the full transparency prevails.
-
Proof of Stake Velocity
Proof of stake velocity is a relatively new addition to the basics of blockchain technology. At present, Redcoin uses this method to validate a block. Here, the process encourages you to have both ownership and activity in the network. These are mainly two functions of this new coin.
In reality, the coin mainly facilitates social interactions in the digital world. However, it’s more power-efficient and fats than typical PoW and PoS.
-
Proof of Elapsed Time
It’s a great consensus algorithm for blockchain applications. However, this one is mainly suited for a permissioned type blockchain network. So, basically not suitable for the public ones. In reality, all the individuals have to wait for a certain amount of time to join a consensus. The time limit is randomly chosen.
Once they finish the wait time, they can then create a block. However, to make sure that the winner chooses the random number, everything is monitored that way.
Moreover, it’s also tracking that if the user did wait for the time, he/she was supposed to.
-
Practical Byzantine Fault Tolerance
Another great consensus algorithm for the blockchain applications. In reality, it mostly depends on the state machine. Even though it follows the same method as Byzantine but still manages to get rid of the general issue.
Before anything happens, the system assumes the possibility of failure and uses other nodes to manage that. Usually, all the nodes in the system are specifically organized. And all the nodes within the network work in a harmony and relay information super-fast.
So, even if a node gets compromised, all the other nodes will know about it quite soon.
Excited to learn blockchain technology and want to become a blockchain architect? Enroll Now: Certified Enterprise Blockchain Architect (CEBA)
-
Simplified Byzantine Fault Tolerance
In the simplified Byzantine fault tolerance algorithm, a group of transactions gets validated at the same time. Usually, the block generator, in this case, collects all the transactions at a time and then batches them accordingly. After grouping them, they get into another block and then that block gets verified.
Before validating any big block, the generator will declare all the rules for the nodes to follow. After that, a block signer uses his/her own signature to validate them. And so, if any of the blocks don’t come with the key, it would get rejected.
-
Delegated Byzantine Fault Tolerance
In this one, the power of the general is limited drastically. While choosing a leader for the army of nodes, the leader would get called the delegate. In any case, if the general tries to be corrupt, another delegate replaces that one.
More so, even the army of nodes can disagree on the leader and can choose another one. SO, as the general would have no sole power, other parties can’t corrupt that node. Moreover, all the nodes may choose a speaker to relay their messages to the delegate.
In reality, to pass a new motion, at least 66% of all the selected delegates would need to agree with the motion.
-
Federated Byzantine Agreement
It’s a rather latest addition to the Byzantine algorithm family. Mainly you will see this one in a network where the transactional costs are pretty low with high scalability and throughput. Moreover, here all the general would get their very own blockchain.
At present, only Ripple and Steller use this method to validate the blocks. However, before any node can request for performance that nodes need to be verified form beforehand. So, the nodes will only choose them that they really trust in this case.
-
Directed Acyclic Graphs
At present, IOTA and NXT use directed acyclic graphs in their blockchain network. Even though many people consider it as a consensus algorithm, in reality, it’s not entirely that. It’s actually a form of data structure.
Furthermore, the data is in topological order other than being in a chain-like format. So, instead of getting one single chain, DAG actually has multiple side chains. Thus, it can validate multiple transactions at a time in parallel. That’s why it takes less time than usual consensus algorithms.
-
Proof of Activity
Proof of activity uses both proof of work and proof of stake to make another hybrid algorithms model. So, the system becomes more robust against any kind of attacks and also uses less power. In reality, the miner mine blocks that are templates rather than complete block.
Furthermore, the block then indicates to a stakeholder that later validates the remaining pre-mined block. Also, the more stake a validator will have, the more valid will his verification be.
At last, all the miners and validators get a fair share of payment from the network.
-
Proof of Authority
Well, this is one of the energy-efficient consensus algorithms on the list right now. However, it suits a private network better than public ones. In reality, only some of the approved accounts can join the validation process.
More so, these nodes are previously approved to be validators. Anyhow a node has to earn the right to validate other blocks and also needs to leave their computer untouched. For doing so, they get rewards on the network to maintain their authority.
-
Proof of Reputation
Another consensus protocol that more suitable for permissioned networks rather than public ones. Usually, in this case, the nodes need to have a good reputational strength to participate in the process. Additionally, the nodes will face severe consequences if he/she tries to cheat in the validation process.
So, not all the nodes can really take part in it. Once the node earns a reputation, then the process is quite similar to the proof of authority.
-
Proof of History
I think you already know how the validation process heavily depends on eth timestamp. But here, you can prove a transaction based on what happened before or after that. So, to do so, you can create a significant event in time that will occur before or after any specific time on the network.
And based on that, others can validate your transaction block. Thus, by doing so, you don’t even need the information of the timestamps in the block.
-
Proof of Importance
Next is proof of the importance consensus algorithm. In reality, it depends on a new factor called vesting or harvesting.
Due to the harvesting, it can determine if a node is eligible to participate or not. So, the more you harvest, the more the chance for the node to become a validator. Also, for the harvesting, the validator gets a reward as the transactional fee. However, the wealthy on the network would have more chance of getting a spot than others.
-
Proof of Capacity
Here, they use the plotting and mining to finish a validation of blocks. Many people also use it instead of proof of work because in this one it takes less time than that. But in PoW you would have to use your computational power even before you start mining.
Even though it’s pretty fast, still, it takes four minutes to mine a block. But I guess you get a six-minute boost. Anyhow, the more plots you have on your computer, the more chance for you to be the mining winner.
-
Proof of Burn
In proof of burn, you would have to burn some of the coins to safeguard the crypto on the network. Obviously, burning the coins would mean a loss. But in the long run, it will keep the network stable. To burn coins, the users will send some of their coins to an eater address.
To make sure everything is in check, the ledger keeps track of all the coins and makes sure they are not usable.
-
Proof of Weight
Proof of weight is actually a massive upgrade form the proof of stake algorithm. Usually, in proof of stake, you see that the more tokens you have, the higher chance of you getting more. In reality, this is a bit biased.
Instead of only taking the tokens into account, the network uses other factors to weigh in. Moreover, these factors are actually the weighted factors that help to determine which nodes get to participate in the system. In short, you get more scalability and faster output here.
Chapter-5: Web3: The New Internet
Understanding blockchain technology is easier than you think. Previously we talked about the layers of the blockchain technology. However, this architecture will actually fuel the next generation of the internet.
Usually, it comes with some of the critical elements that we will see.
Now we will talk more about it for understanding blockchain technology a bit better.
Let’s start!
-
Artificial Intelligence
Well, first of all, this is definitely not about super robots. In reality, the AI will ensure a better output when it comes to results and analysis of the data on the ledger. Even though it might not sound like a big deal, but the experience will drastically change.
Typically it will make sure that you get to the content that you are looking for on the internet. So, that means more accurate results, better forecasting of your actions. In reality, it’s just a simple mechanism that helps to learn about your tastes and give you’re the best output base do that.
Curious to know more about the fundamentals of enterprise blockchains? Enroll Now: Enterprise Blockchains Fundamentals – Free Course
-
Ubiquity
For understanding blockchain technology better, you would need to know what the ubiquity is really about. Just look around you and see what all the people are using any kind of device to use the internet.
Moreover, all the smart TV, fridge, smart home accessories, assistants, tabs, or smartphones do the same thing. So, they all connect to the internet. By doing so, they form a network. Usually, this network is actually called the Internet of Things. However, in some cases, people call it ubiquity.
Anyhow, the future of the internet depends a lot on this process.
-
Enhanced Connectivity
The new internet web 3.0 is based on the fact that it would be user-centric. So, it means that you will see more connectivity than you see in web 2.0 internet. Additionally, no one will control your data or use it for their personal gain.
Here, the semantic metadata is of big help. In reality, it helps the users to stay connected more easily and quickly. Thus, it enhances connectivity.
-
Semantic Web
For understanding blockchain technology, you need to know about the semantic web as well. It’s a massive part of the web 3.0 internet. Furthermore, semantic web actually means the understanding process of any web content similar to humans.
Thus, it will depend on machine learning and will not focus on keywords only. So, if you have good content and do not depend on the keywords, you are going to have a good amount of crowd.
-
3D Graphics
Well, obviously 3D graphics are a huge part of understanding blockchain technology web 3.0. As you can see now, people like to see images, videos instead of reading any texts. So, the best way to increase focus would be to have 3D graphics integrated to it.
All the apps in the future will use some form of Virtual Reality or Augmented reality
-
Peer-To-Peer Network
The new internet will be totally decentralized. So, there is no option for any kind of centralized authority ruling over what you do and what you don’t. But that clearly doesn’t mean that you can break all the laws here.
This is just an element that will ensure all your data online will remain safe no matter what.
Excited to know more about peer-to-peer network? Read this article: Understanding Peer To Peer Network
Chapter-6: Examples of Enterprise Blockchains
Now that you know all about blockchain technology, it’s time for you to take a look at the popular enterprise blockchain platforms on the market. Let’s see what they are, shall we?
Hyperledger
Hyperledger is one of the best blockchain platforms that you can use in almost any kind of sector. Really, any kind! Even if you are looking for blockchain technology in banking, you can rely on this one. Not to mention the extreme popularity of Hyperledger blockchain technology. And why wouldn’t it be popular?
It offers some of the most lucrative features on the market –
- Modular architecture that lets you plug into any kind of application and use it.
- Permissioned network that you can use to add privacy in your network.
- High scalability ensures that you enjoy the best performance for all time.
- Safety protocols that will safeguard your information.
- Data availability based on the need to know the concept.
Ethereum Enterprise
Ethereum is another one of the popular blockchain platforms on the market suited just for enterprises. In reality, Ethereum is also great for all kinds of industry. However, as its public, it might not be suitable for blockchain technology in banking.
But its commercial version Ethereum Enterprises offers a private channel in the architecture. So, that version is most suitable for blockchain technology in banking. Anyhow, it provides –
- Governmental support as you implements new projects based on Ethereum.
- An open platform that you can use without any issues.
- Fast upgradations to introduce newer additions and fix bugs better than others.
- Offer standards to help other companies build their very own network.
Want to develop expertise in Ethereum Space? Enroll Now: The Complete Ethereum Technology Course
R3 Corda
Corda comes with two different versions – enterprise Corda and Corda. In reality, the enterprise Corda is most suited for any kind of enterprise use cases. However, many people consider this tech to be a blockchain technology in banking. But as time goes by, Corda is becoming popular in other industries as well.
It offers some of the lucrative features such as –
- Blockchain application firewall that safeguards the whole network form any kind of cyber-attack.
- High-Availability that ensures that your network stays up and running 24/7.
- Governance system, which will allow enterprises to have rules in the system.
- The monitoring system that allows any user to locate any disasters and recover them.
Want to learn everything about Corda? Enroll Now: Beginner’s Guide To Corda Development
Ripple
Well, Ripple is another blockchain technology in banking that’s more suited for financial sectors at present. The best part about Ripple is that it offers an almost free transaction platform. Furthermore, in the case of the financial sector, it does provide a relatively faster output.
The platform is so fast that you can settle the payment within only 4 seconds! It offers –
- New marketplaces that help to get revenue quickly.
- Reaches out to more consumers within a short amount of time promoting an excellent growth rate.
- Scalability that makes sure your system offers the same performance under pressure.
- Permissioned platforms that offer more privacy.
- High level of security, which fights off cyber-attacks.
Quorum
Quorum came when the enterprises were looking for a good solution that can ensure their full confidentiality. In reality, J.P. Morgan introduced it to the world in 2017. But why is it so popular? Well, it comes with a unique way to get all the blocks verified. Instead of depending on typical power-consuming ones, it offers a faster and better algorithm.
Anyhow, it offers –
- Private transactions that would let you transact with another party in a secure channel.
- Permissioned network, which makes sure that your personal transactions are safely away from the ledger.
- Node management that will let you choose which nodes can enter the network.
- High scalability for a better experience.
- The faster settlement that saves time.
Chapter-7: Concluding Thoughts
Blockchain technology is relatively one of the coolest innovations of all time. Just 10 years earlier, we didn’t even know that decentralized applications could ever be possible. But now look at the tech industry. Everyone is looking for a way to integrate this new system into their existing one.
In reality, it would take more time to completely replace the old centralized structure and get used to the new one. But I can safely say that it won’t be a bad experience at all.
Want to know everything about blockchain? Enroll now for blockchain certification and courses.