Learn how blockchain truly works, master key definitions, and uncover what makes smart contracts so "smart." Dive into the fundamentals, gain valuable insights, and start your blockchain journey today!

- Decentralized Finance
James Howell
- on December 29, 2022
Top 10 DeFi Hacks You Should Know
Decentralized Finance (DeFi) involves the use of blockchain applications for removing conventional intermediaries from the financial services ecosystem. While DeFi has been responsible for introducing massive changes in accessibility, the risks of DeFi attacks have been raising concerns.
How big are these concerns about DeFi security? The total amount lost to DeFi theft in 2021 was $1.5 billion. Within the first few months of 2022, DeFi hacks accounted for almost $1.4 billion in losses. It is important to understand that DeFi is not a random trend in technology. As a matter of fact, it is the new definition of the financial ecosystem of the future.
The significance of DeFi security is clearly evident in the number of financial losses incurred by users. Therefore, it is important to identify the causes behind top DeFi hacks and work on developing preventive measures. The mainstream adoption of DeFi depends on the effectiveness of safeguards against DeFi hacks. The following discussion helps in identifying how hackers exploit DeFi protocols, along with detailed coverage of top DeFi exploits. In addition, you can also reflect on the necessity of safeguarding DeFi protocols and tokens.
Want to know more about DeFi? Enroll Now in our Introduction To DeFi – Decentralized Finance Course!
Why Should You Learn about DeFi Hacks?
Decentralized finance has drawn considerable criticism in recent times owing to the increasing frequency and magnitude of attacks. The concerns of a DeFi exploit could prevent users from adopting DeFi protocols. DeFi started off with cryptocurrencies, and the domain has expanded with the introduction of dApps for staking, lending, and borrowing, as well as decentralized exchanges.
As of September 2022, the total value of assets locked in DeFi protocols was $53.73 billion. The number of losses to DeFi hacks had escalated to almost $2.32 billion by this time. With such a humongous scale of losses, the list of DeFi hacks has inflicted 50% higher damage on the DeFi industry as compared to 2021.
Another alarming aspect of DeFi hacks refers to the gradually declining TVL in the DeFi market. According to DappRadar, the TVL in DeFi had reduced to $41.54 billion by November 2022. Looking back at 2021, the TVL estimate was over $110 million, thereby suggesting a radical decline. One of the common reasons presented for the reduction in TVL points to the recent collapse in stablecoin value.
On the other hand, financial losses incurred due to vulnerabilities in DeFi protocols and tokens could also be one of the factors responsible for reducing TVL. Some of the most popular DeFi hacks have been targeted at the commonly used DeFi protocols. The losses due to DeFi exploits can create a general loss of trust in the feasibility of DeFi as an alternative to traditional financial services. Most important of all, the value locked in DeFi serves as an appealing target for hackers. Therefore, it is important to learn about DeFi hacks to avoid unwanted consequences of security breaches in DeFi protocols.
Learn the fundamentals of Decentralized Finance (DeFi) with DeFi Flashcards
How do Hackers Exploit DeFi?
Before diving into a DeFi hacks list, it is important to identify the ways in which hackers exploit DeFi protocols. What could be the potential causes for vulnerabilities in DeFi?
- The foremost source of vulnerability in DeFi refers to its open-source nature, which exposes the code to everyone. While the open-source nature ensures the benefits of transparency, it also opens up multiple avenues for hackers to exploit the protocols.
- Another common cause underlying DeFi attacks refers to the principle of composability, which exposes DeFi protocols to external exploitation.
- The next reason for vulnerabilities in DeFi is the pace of launching.
- Developers are more likely to ignore vulnerabilities and errors in a bid to launch their protocol before competitors.
Hackers can exploit these vulnerabilities and gain unauthorized access to the assets of DeFi users. How do DeFi hacks happen? The assessment of various DeFi hacks could showcase some of the possible ways in which hackers compromise DeFi protocols. Some of the common methods for DeFi hacks include the following,
-
Oracle Manipulation
Hackers could manipulate the oracle smart contract, used in DeFi protocols for obtaining external information. One of the common exploits through oracle manipulation involves changing token price details.
-
Smart Contract Logic Errors
The urge to push DeFi protocols to the market at a faster pace is one of the notable causes for a DeFi exploit, as developers miss trivial vulnerabilities and errors. Since the DeFi protocol code would be open-source, attackers could see the smart contract code and identify the glitches for exploiting them.
-
Reentrancy Attacks
Another common method followed in DeFi hacks points at reentrancy attacks. Such attacks involve a smart contract calling an untrusted contract externally without resolving it.
Curious to understand the complete smart contract development lifecycle? Join Standard/Premium Plan and get free access to the Smart Contracts Development Course Now!
Most Popular DeFi Hacks
DeFi vulnerabilities are one of the biggest threats to the community. Apart from the direct impact of financial losses, the continuously growing list of DeFi hacks also affects the reputation of DeFi startups. Therefore, it is important to take a look at the details of the following top hacks in the DeFi landscape.
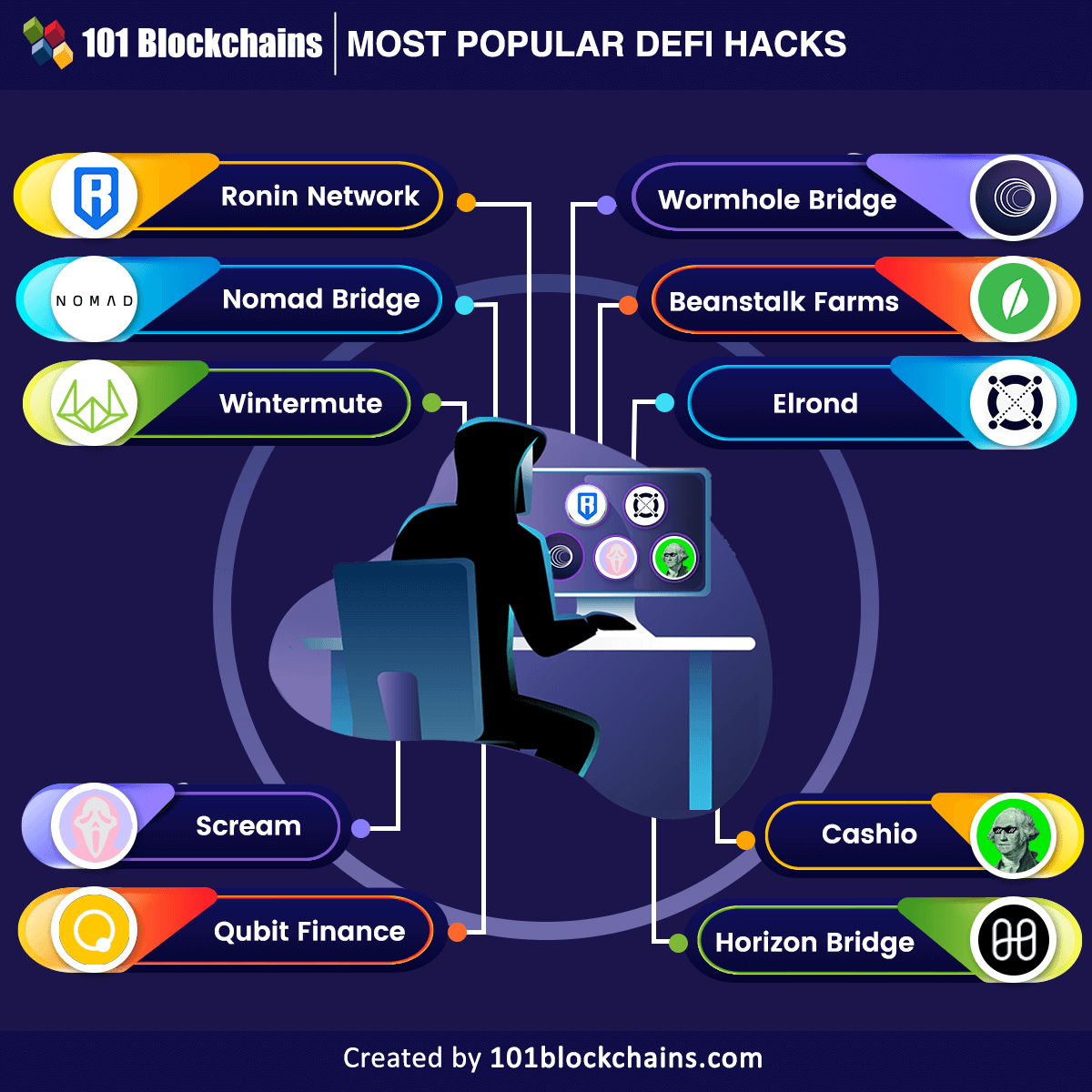
Ronin Network
Ronin Network is the Ethereum based sidechain of a popular play-to-earn game, Axie Infinity. It incurred a loss of more than $625 million in ETH and USDC assets in a hack. You can develop a better understanding of the hack by understanding how the Ronin Network works. Ronin was designed to help Axie Infinity players enjoy the game without the complicated interactions with the Ethereum blockchain. The Ronin Bridge served as an effective channel for players to transfer their ETH to the Axie Infinity network.
The Ronin Bridge was responsible for one of the top DeFi hacks, as attackers compromised the bridge and forged fake withdrawals. The attacker utilized the hacked private keys for withdrawing assets in two different transactions. The attacker gained unauthorized control over five validators required for releasing funds on the Ronin Bridge. Even if the exploit had happened on March 23, Axie Infinity had not reported it for almost a week. The attacker had compromised around 25.5 million USDC and 173,600 ETH in one of the biggest hacks in DeFi history.
Want to learn about the Ethereum Technology? Enroll now in The Complete Ethereum Technology course.
Nomad Bridge
The next addition among the most popular DeFi hacks would refer to the Nomad Bridge hack. Hackers stole almost $190 million from the cross-chain bridge, which helps in swapping tokens such as Ethereum, Moonbeam, Avalanche, and Evmos. Interestingly, the attack on Nomad Bridge was not carried out in one or two transactions. Apparently, the attack involved 1175 hacks and was one of the first in which many hackers copied the same exploit. The attack was attributed to an upgrade in the code of Nomad, which exposed a vulnerability in which a specific section was marked valid for all transactions.
The original hacker found this vulnerability, and many other copycats joined in without much effort. All the attackers copied the transaction call data of the original hacker and mentioned their address in place of the original address. Subsequently, the hackers withdrew more assets than the ones deposited on the platform. Interestingly, the Nomad team requested the return of funds through an open message, and some of the white hat hackers responded by returning around $30 million.
Build your identity as a certified blockchain expert with 101 Blockchains’ Blockchain Certifications designed to provide enhanced career prospects.
Wintermute
The Wintermute hack is also one of the notable mentions in a DeFi hacks list, with a loss of almost $160 million. Wintermute used an address-generating tool for creating unique addresses that would reduce transaction costs. However, these addresses were vanity wallet addresses featuring 32 characters. Any hacker with the right set of resources could have made their way into the protocol for recreating the private keys in an address.
The prominent cause of the Wintermute hack points to the possibility of their DeFi vault and hot wallet contract having vanity addresses. Hackers could easily access the funds in these sources and move them according to their convenience. Wintermute tried removing all ETH from its hot wallet in an attempt to stop the hack. However, they had not removed the address of the admin for their vault. Even though the details of the hack are still under the shadows of doubt, hackers must have made away with everything they found in the hot wallet.
Wormhole Bridge
The Wormhole Bridge is another prominent entry among DeFi attacks on a bridge. Wormhole Bridge does not serve as a game exchange like Ronin Bridge. On the contrary, it works as a token bridge through which users can exchange tokens across multiple blockchains, such as Ethereum, Terra, Oasis, Solana, and Avalanche. Users of the bridge have to stake their ETH and receive wrapped ETH in return, which would have a backing of 1:1 ETH liquidity. As a result, the network would also include the wrapped ETH in the same range as normal ETH. Apparently, hackers decided to leverage the liquidity to attack the protocol.
The Wormhole Bridge attack offers better insights on “How do DeFi hacks happen?” with faults in the ‘guardian’ accounts. In a unique approach for DeFi hacks, the hacker minted around 120,000 wrapped ETH tokens on Solana without any ETH backing. Then, the hacker siphoned around 93,750 of the wrapped ETH tokens into the Ethereum network and redeemed around $254 million. With these funds, the hackers purchased different tokens, such as Finally Usable Crypto Karma and Bored Apes. The Wormhole Bridge attack draws attention to the fundamental security challenges with crypto bridges.
Beanstalk Farms
Beanstalk is an algorithm-based stablecoin protocol that does not rely on a liquidity pool. It experienced one of the biggest losses with a DeFi hack in April, which cost the protocol around $182 million. The Beanstalk Farms DeFi exploit suggested how simple security vulnerabilities in DeFi tokens could result in formidable losses. The primary reason for the Beanstalk hack was its own decentralized governance protocol and the facility of flash loans.
With the flash loan, the hacker obtained a majority stake in the governance mechanism and siphoned crypto assets out of the protocol to different addresses. The Beanstalk Farms hack clearly emphasizes the fundamental vulnerability in the Beanstalk DAO.
Want to understand the best ways to use DeFi development tools like Solidity, React, and Hardhat? Enroll now in DeFi Development Course!
Elrond
The Elrond hack also qualifies as one of the top DeFi hacks, with a loss of around $113 million. Hackers used a loophole in Maiar, a decentralized exchange, to steal almost 1.65 million in EGLD tokens, the native token of the Elrond blockchain. According to reports, the hacker used a smart contract alongside three wallets to steal EGLD from the decentralized exchange.
On top of it, the hackers quickly sold around 800,000 of the native tokens of the Elrond blockchain for almost $54 million on Maiar itself. The hackers sold off the remaining tokens on centralized exchanges and swapped some of them in return for ETH.
Scream
Another notable entry among the victims of DeFi hacks would refer to Scream, a DeFi lending platform. Based on Fantom blockchain, the Scream hack suggests one of the most juvenile exploits, especially considering the flaws in protocol security. The platform ended up with a debt of almost $38 million following a decline in the peg of stablecoins on the platform, such as DEO and Fantom USD.
The Scream protocol hack qualifies as one of the most popular hacks due to the simple yet ambiguous loophole for the attack. Scream protocol hardcoded the value of the two stablecoins without any adjusting mechanisms. Therefore, it was not able to display the declining value of the assets.
Whales exploited the loophole to draw out valuable stablecoins as they deposited the DEI and Fantom USD stablecoins which were losing value. Scream protocol introduced Chainlink oracles for obtaining access to real-time pricing data as a replacement for hardcoded stablecoin pricing.
Learn the fundamentals of Blockchain through Blockchain Basics Flashcards
Qubit Finance
The Qubit Finance DeFi protocol announced on January 28 that a hacker had compromised around 206,809 BNB or Binance tokens. The protocol informed that its QBridge protocol was the primary site of the attack, and the total value of compromised tokens amounted to almost $80 million.
It is also one of the significant entries in a DeFi hacks list, with a significant loss. The hacker discovered a vulnerability in the QBridge contract through the deposit option and minted around 77,162 qXETH, which represents the ETH bridged through Qubit.
If you look closely, the hacker made the platform believe that they made a deposit and repeated the process many times. Finally, the hacker exchanged the assets on the protocol for BNB tokens and disappeared into thin air.
Horizon Bridge
Crypto bridges did not have a good year in 2022, and the Horizon Bridge hack proved the same. The Horizon Bridge suffered a DeFi hack on June 23, inflicting damage of around $100 million. Horizon offers a cross-chain interoperability platform that facilitates seamless usability between multiple blockchain networks such as Ethereum, Harmony, and Binance Smart Chain.
The evaluation of the DeFi exploit pointed out that hackers had moved out $98 million from the Harmony-managed platform. Hackers exchanged the tokens for ETH, affecting more than 50,000 wallets. Subsequently, the hackers also leveraged Tornado Cash to move out almost $35 million.
Cashio
Just like crypto bridges, stablecoin protocols got featured in the list of DeFi hacks quite frequently. Cashio is another example of a stablecoin protocol that was a victim of DeFi hacks this year. The hack resulted in the decline of the CASH stablecoin of the protocol with losses of almost $48 million. Cashio enables minting CASH stablecoin through deposits with the backing of interest-bearing liquidity provider tokens.
The hacker used the basic functionality of Cashio to mint billions of CASH, followed by exchanging them for UST and USDC. Subsequently, the hacker withdrew the tokens by using the Saber DEX. As a result of this hack, the CASH stablecoin died off after crashing to $0.
Want to learn the basic and advanced concepts of Stablecoin? Enroll in our Stablecoin Fundamentals Masterclass Now!
How Can You Prevent DeFi Security Attacks?
The scale of losses incurred by DeFi protocols due to different hacks calls for immediate attention to safeguards for DeFi. Many DeFi protocols feature incentives for improving security, while some use practical solutions for preserving DeFi security. The impact of the top DeFi hacks on users and the community also draws the limelight on following DeFi security best practices. For example, smart contract security audits or comprehensive penetration tests for DeFi protocols. In addition, protocol developers could also implement bug bounties and interact with communities of external security experts for the safety of protocols.
Decentralized Finance is now considered a better alternative to centralized Finance. Learn how it works and elements of the DeFi ecosystem through AN INTRODUCTION TO DECENTRALIZED FINANCE (DEFI) Ebook
Bottom Line
The outline of the most popular DeFi hacks reflects the dire state of security in the DeFi ecosystem. The common targets for the DeFi hack included stablecoin protocols and crypto bridges. While interoperability is a major positive highlight for DeFi protocols, the hacks make it look like a setback.
Therefore, it is important to understand the answers to “How do DeFi hacks happen?” through a detailed assessment of various hacks. Clarity regarding the common errors and vulnerabilities affecting DeFi protocols could help in avoiding massive losses. Effective resolution of DeFi security risks is to offer users safety and encourage trust in DeFi. So, start learning more about DeFi and how it works to understand the security risks in detail.
*Disclaimer: The article should not be taken as, and is not intended to provide any investment advice. Claims made in this article do not constitute investment advice and should not be taken as such. 101 Blockchains shall not be responsible for any loss sustained by any person who relies on this article. Do your own research!



![30+ Best Decentralized Finance Applications [Updated] best decentralized finance (DeFi) applications](https://101blockchains.com/wp-content/uploads/2020/10/decentralized-finance-applications.png)