Learn how blockchain truly works, master key definitions, and uncover what makes smart contracts so "smart." Dive into the fundamentals, gain valuable insights, and start your blockchain journey today!

- Blockchain
Diego Geroni
- on May 05, 2021
How Does Blockchain Use Public Key Cryptography?
The importance of security is evident more than ever in the present times. The formidable growth and expansion of computer networks all over the world have resulted in a radical escalation of the volumes of sensitive information moving across systems throughout the world. At the same time, we have a new decentralized, distributed digital ledger network, i.e., blockchain technology, at our disposal.
While blockchain itself offers the inherent advantage of the security, it is important to understand the significance of public key cryptography in blockchain. Public key encryption has emerged as a promising alternative to the conventional symmetric encryption techniques. The following discussion attempts to showcase the use of public key encryption in the blockchain.
Build your identity as a certified blockchain expert with 101 Blockchains’ Blockchain Certifications designed to provide enhanced career prospects.
Understanding Public Key Encryption or Cryptography
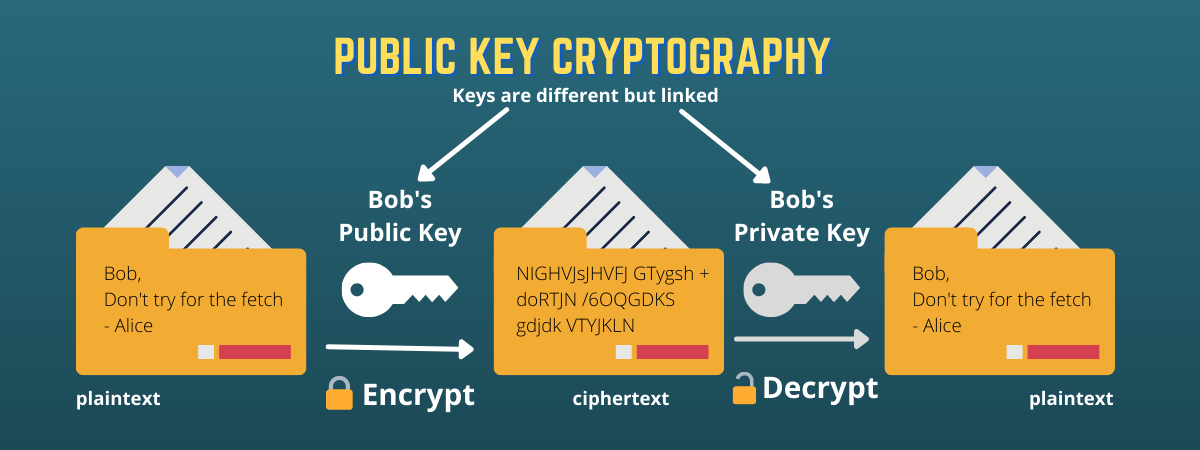
The foremost aspect that is required to understand encryption with public key in blockchain refers to the definition. Public key encryption, otherwise known as asymmetric cryptography, refers to a collection of cryptographic protocols that rely on algorithms. The cryptography method involves using two different keys, such as a private key and a public key.
The private key is secret for every participant in a network and is unique for them, while the public key is visible to all participants in the network. The applications of public key cryptography leverage the pair of keys for encryption and decryption of data to avoid unauthorized use or access. Certification authorities provide public and private key pairs to network users.
Users who want to encrypt data before sending it will have to obtain the recipient’s public key. The public key can help in encrypting a message before sending it to the concerned recipient. When the recipient gets the message, they can use their private key for decrypting the message. It is essential to remember that only the recipient knows about the private key. Therefore, the applications of public key cryptography ensure that the valuable information of users is not tampered with in transit.
Public key encryption leverages the RSA or Rivest-Shamir-Adleman algorithm for transmission of secure and highly sensitive data across an insecure network. The RSA algorithm has achieved profound popularity because of support for using public and private keys for message encryption. At the same time, the RSA algorithm can also ensure better safeguards for confidentiality and authenticity of the public and private keys.
Want to become a Cryptocurrency expert? Enroll Now in Cryptocurrency Fundamentals Course
Why Do We Need Public Key Cryptography?
So, why is it important to consider the use of public key approach for blockchain cryptography? What is the problem with conventional secret key systems? Contrary to the general assumption, public key encryption is not tailored for replacing traditional private key cryptography. As a matter of fact, public key encryption emerged as an answer for the shortcomings in secret key-based systems.
Basically, public key or asymmetric cryptography discovers applications in scenarios where private key cryptography does not serve the required results. Public key encryption becomes important in cases that involve a massive number of users. Generally, public key cryptography is suitable for multi-user environments that focus on ensuring confidentiality through digital signatures and key distribution.
Public key encryption provides noticeable benefits in comparison to symmetric private key encryption systems. First of all, it takes away the need to address the logistics and risk concerns associated with swapping keys secretly. In addition, it also provides better security and scalability in comparison to symmetric encryption. As a result, it continues to enjoy the reputation of the most popular cryptographic technique available presently for enterprise environments.
Excited to know about the hashing in cryptography? Read here for a detailed guide on Hashing In Cryptography now!
Public and Private Key Pair
Now, it is important to reflect on the different components of public key encryption. It will help in deriving a clear impression of the potential applications of public key cryptography in blockchain. The private key leveraged for public key encryption basically represents a random number having specific properties. Users can derive the public key from the private key.
The keys are capable of ensuring security in public key encryption through the foundations of mathematically complicated issues. The basic notion underlying the use of public and private keys is to ensure ease of performing cryptography and difficulty in reversal. As a result, public key encryption process features polynomial complexity as well as exponential complexity.
Some of the generally used hard problems include the factoring problem or the discrete logarithm problem. Factoring problems involve encryption through the multiplication of two prime numbers that are easier while offering difficulties in factoring. On the other hand, discrete logarithm problems can involve easier exponentiation while presenting difficulties with logarithms.
The difficulty of the problem is an essential requirement for maintaining the perfect balance between usability and security. It is important to note that some operations could be easier than others. Therefore, the applications of public key in blockchain can help in designing algorithms that permit authorized users to carry out easy operations and force unauthorized intruders to execute hard tasks. It is easier to adjust the difficulty of problems by just increasing the size of values used in the problem. As a result, it can ensure that the system is immune to any potential attacks while also offering the desired usability.
The aim of public key encryption with the use of different keys focuses on serving different purposes such as encryption and digital signatures. Encryption is an important function of public key cryptography in blockchain. As the world is slowly coming to terms with newly emerging concepts of security and privacy, encryption bears a larger significance. Any individual with knowledge about the public key of a user could carry out the encryption of a message with it.
The other notable application of public key encryption in the blockchain is visible in digital signatures. Digital signatures enable signing a document or message digitally with a private key that enables verification of the signature with the related public key. The two operations of encryption and digital signature utilize similar algorithms. However, the notable factor, in this case, refers to the use of one key for undoing the action of the other key, i.e., deriving the original message.
Want to understand the difference between Private & Public Key? Check here a Newbie’s Guide: Private Key Vs Public Key – How They Work now
Applications of Public Keys in Blockchain Cryptography
Now, let us arrive at the most important point of discussion on our agenda in reflecting on the use of public keys in blockchain for cryptography. Blockchain has been tailored as a distributed and decentralized network. All nodes in the network take on the responsibility for the maintenance of their own copy of the digital ledger. In addition, blockchain also ensures the transmission of data in the shape of blocks and transactions among the nodes through a peer-to-peer network.
However, blockchain adoption depends a lot on the feasibility of fundamental benefits of security, transparency, and control. Public key cryptography and digital signatures are highly critical for ensuring the effective functioning of security in blockchain systems. Public key encryption can allocate the following distinct features in the blockchain landscape.
1. Authentication
Authentication is one of the critical aspects that establish the formidable foundation for blockchain cryptography. Digital signatures can provide adequate proof regarding the fact that a message has been created by an individual with proper awareness regarding the relevant private key. The association of public keys with specific accounts ensures that only an individual with knowledge regarding the account’s private key could create transactions starting from the concerned account.
2. Integrity Protection
The second important application of public key cryptography in blockchain refers to integrity safeguards. Blockchain transactions generally involve the transmission of a specific transaction or block through multiple nodes. The transaction or block has to cross all nodes starting from the origin to a specific node in the network. Now, it is important to note that blockchain has been created specifically to reduce the need for trust in other nodes.
Therefore, it is highly crucial to ensure that the data of a transaction or block is safe from any unauthorized, malicious intervention. In addition, digital signatures are able to achieve validity only in event of zero modifications or tampering with the associated data. As a result, public key cryptography could provide the assured benefits of authentication as well as integrity protection with ease.
3. Identity Management
The applications of public key encryption in blockchain also find a formidable mention for identity management. Public key cryptography helps in identity management on the blockchain. Since the account addresses are based on public keys, it is easier to create valid accounts only through creating private/public key pairs and the related address.
As a result, blockchain users could remain anonymous as the private key is just a random number without any links to the real identity of users. At the same time, blockchain cryptography also ensures proper authorization of all transactions made through the concerned account. Since all the authorized transactions on blockchain carry valid digital signatures, it enables easier verification of transaction authenticity.
Start your blockchain journey Now with the Enterprise Blockchains Fundamentals
Advantages of Public Key Encryption for Blockchain
Based on the distinct applications of public key cryptography in blockchain, any individual could find out the benefits. However, public key encryption has more wide-ranging benefits at its disposal. First of all, public key encryption enables better data security. It is still one of the most secure protocols in comparison to private key cryptography for various reasons.
Public key encryption does not demand any transmission or exposure of private keys to other individuals. Therefore, it can ensure that cybercriminals cannot discover a person’s secret key during the transmission of information over blockchain networks.
Public key cryptography also ensures non-repudiation of transactions. It implies that every user must bear the responsibility of safeguarding their private key. On the other hand, private key systems demand that users must share their secret keys and trust third parties in certain cases for ensuring transmission.
Implications of Public Key Encryption in Blockchain
Blockchain cryptography relies profoundly on the public key approach. As discussed already, it involves two different keys, with each pair having its own uniqueness. In addition, it is also important to note that asymmetric cryptography algorithms develop key pairs linked to each other mathematically. So, it is reasonable to encounter longer key lengths in comparison to the shared secret key used in symmetric encryption.
The longer length of the key, generally in the range of 1024 to 2048 bits, creates profound difficulties in drawing a private key from the public key. The most common algorithm utilized for public key encryption, i.e., RSA algorithm, features the creation of keys through the multiplication of large prime numbers.
Public key encryption is capable of resolving profound problems of encryption. The communication keys used for encryption and decryption are different from each other in public key encryption. On the other hand, the sharing of the single secret key over insecure connections can expose the key to unauthorized third parties. Subsequently, the unauthorized parties could view all the messages encrypted with a shared key.
Symmetric encryption approaches have been leveraging the power of cryptographic techniques to solve the problem. However, they still present prominent risks for the security of the keys. In the case of public key cryptography, it is easier to share the key used for encryption throughout the network. Therefore, it is possible to achieve better protection with a public key or asymmetric cryptography in comparison to symmetric encryption.
Limitations of Public Key Encryption in Blockchain
Finally, it is also important to reflect on the limitations associated with public key encryption. The limitations can help in understanding the extent to which it will be usable for blockchain applications and networks. The foremost setback with public key cryptography in blockchain comes with the problem of algorithms slowing down when dealing with massive volumes of data.
In addition, the success of public key encryption depends considerably on the ability to maintain private key in secrecy. Users could accidentally lose their private keys, thereby losing access to encrypted data. At the same time, the private key repositories are highly vulnerable to malicious attacks, thereby resulting in compromised private keys.
Curious to learn about blockchain implementation and strategy for managing your blockchain projects? Enroll Now in Blockchain Technology – Implementation And Strategy Course!
Final Words
On a final note, it is reasonable to find out a reasonable connection between the applications and benefits of public key cryptography and blockchain. Blockchain is emerging as a promising technology for the future with prominent value propositions for enterprises, governments, and individuals. So, it is quite important to reflect on the security concerns associated with blockchain.
Public key encryption or cryptography provides the advantages of secure verification of ownership and secure transmission of data. Furthermore, public key encryption also empowers blockchain with potentially resilient algorithms that ensure data integrity and privacy. With all the benefits of cryptography for blockchain, careers in blockchain security are on the rise. Take a look at the opportunities you can have with the 101 Blockchains Certified Blockchain Security Expert (CBSE) certification now!
*Disclaimer: The article should not be taken as, and is not intended to provide any investment advice. Claims made in this article do not constitute investment advice and should not be taken as such. 101 Blockchains shall not be responsible for any loss sustained by any person who relies on this article. Do your own research!