Learn how blockchain truly works, master key definitions, and uncover what makes smart contracts so "smart." Dive into the fundamentals, gain valuable insights, and start your blockchain journey today!

- Guides
101 Blockchains
- on July 07, 2019
Hashgraph and Hedera Hashgraph: Everything You Need To Know
If you want to learn about Hashgraph technology, then you have come to the right place. We will go through it in detail and also look into its public implementation, the Hedera Hashgraph.
Decentralized Ledger Technologies(DLT) — It is one of the most searched terms in 2018. And why not? This is what changing the way we are solving the problems around us. Companies and startups have already learned the importance and integrating blockchain into their workplace. So, does it mean that blockchain is the ultimate solution for companies that are looking to transform their business? Well, not really.
Want to become an expert in Hedera Network Services? Enroll Now in Hedera Fundamentals Course!
Meet Hashgraph.
Hashgraph is a DLT(distributed ledger technology) that offers a different approach in solving the decentralized solution. It is developed by the CTO and the co-founder of Swirlds, Leemon Baird. If you are entirely new to distributed ledger technology, you may find Hashgraph slightly confusing or just need time to a clear idea. However, if you are into blockchains, you may find striking similarities between blockchain and Hashgraph — the two most popular DLTs out there.
Blockchain Technology
Before we move on to understand Hashgraph, we must need to get a glimpse of what blockchain technology has to offer. First things first, it is one of the most popular distributed ledger technology out there. Many cryptocurrencies utilize blockchain technology. However, not all of them use the “chains of block” concept.
Blockchain networks are basically peer-to-peer networks that are managed by peers. The crucial difference here is how the network is maintained. They are entirely decentralized, and no authority handles the network. The trust is gained with the help of the consensus algorithm and database replication.
The key concept here is the “blocks.” The transactions(records) are stored in blocks, and they are mostly done in chains, and there is no way a data can be modified in any possible way. This makes the blockchain technology ideal for storing records, asset management, voting, and so on.
The problem with blockchain
Blockchain has evolved a lot in the past decade. It all started with bitcoin which offered the first ever version of blockchain. It is the first generation of blockchain that introduced the concept of decentralized ledger technology. It was fascinating in its own way and ground-breaking to say at least.
One of the major problems that the modern blockchain-based solution is the transfer speed associated with them. Ethereum, one of the new blockchain-based DLT, offers 15 transactions per second. Bitcoin, on the other hand, is not impressive as well. It provides only 5 transactions per second. That’s a significant disadvantage when it comes for business to adopt the blockchain technologies.
Build your identity as a certified blockchain expert with 101 Blockchains’ Blockchain Certifications designed to provide enhanced career prospects.
What is Hashgraph? A sneak-peak behind the Hashraph technology
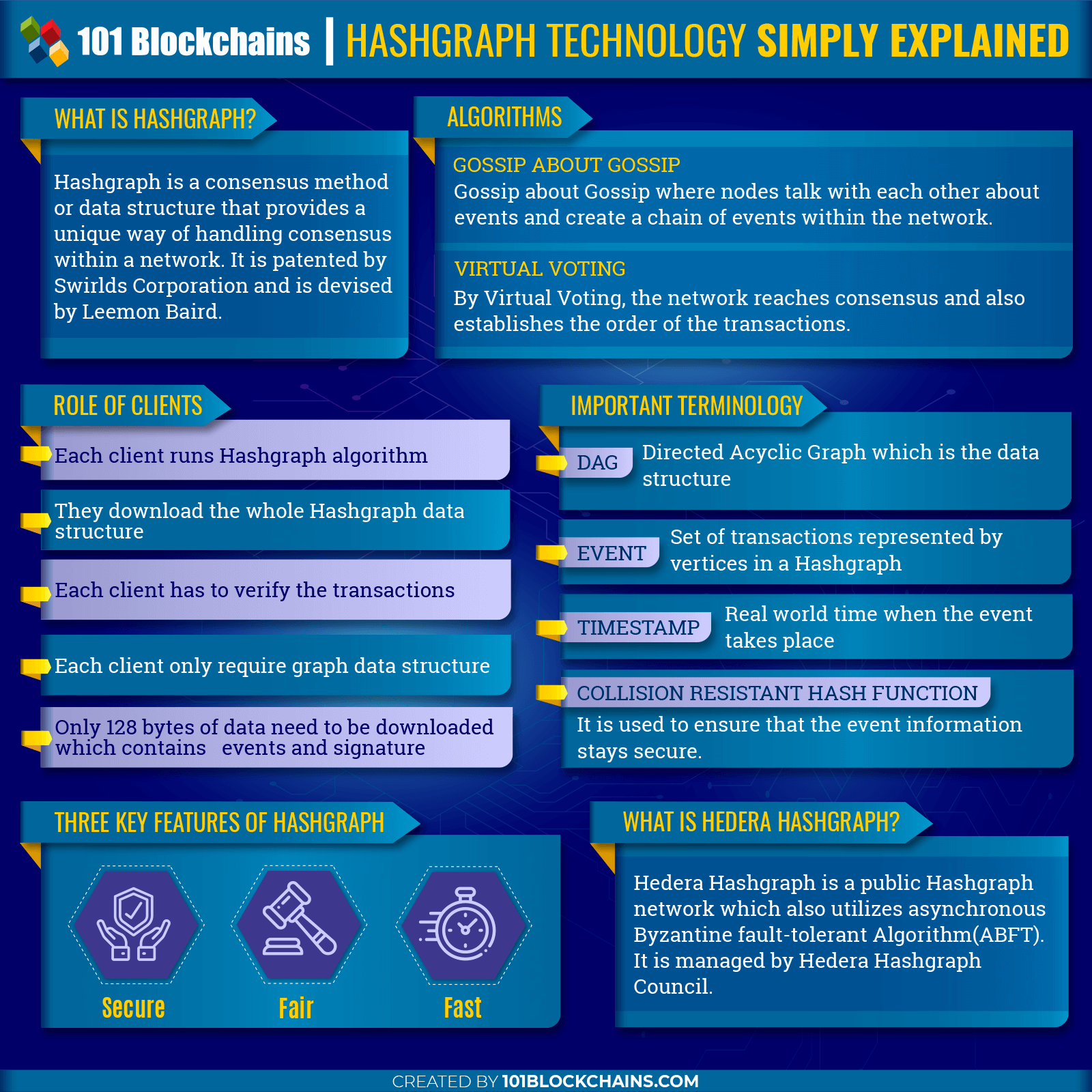
Please include attribution to 101blockchains.com with this graphic. <a href='https://101blockchains.com/blockchain-infographics/'> <img src='https://101blockchains.com/wp-content/uploads/2019/06/HASHGRAPH.png' alt='HASHGRAPH='0' /> </a>
Hashgraph is yet another distributed ledger technology. It is a patented technology that is devised by Leemon Baird and licensed under the Swirlds Corporation. Hashgraph is an improved version of DLTs which offers security, distribution, and decentralization with the use of hashing. This means it doesn’t suffer from the speed problem.
Hashgraph is capable of processing thousands of transactions per second, and this is what differentiates it from blockchain technology. There are also many Hashgraph use cases out there including using it in cryptocurrency.
However, the speeds are obtained because of its private nature. There is also a public version of Hashgraph which is the Hedera Hashgraph — another Hashgraph use cases. It also falls within Hashgraph applications category. We will talk about the Hedera Hashgraph in the later section of the article. So, stay tuned!
Clearly, if you go through the Hashgraph whitepaper that released in May 2016, you will notice that it defines itself as a “consensus algorithm” or “system”, and not exactly a distributed ledger technology. We also agree to the definition of its being a data structure or a consensus algorithm rather than a complete system. The reason behind it is that it can be seen as a low-level building block. However, later in the guide, we will cover Hedera Hashgraph that seems to be a complete solution.
Hashgraph Explained: Technology Overview
So, what makes Hashgraph Technology tick? What makes it faster, more secure and fair among the DLT landscape? Let’s explore.
Hashgraph lacks “chain of blocks.” To improve overall efficiency, Hashgraph technology uses two algorithms. They are as follows:
- Gossip about Gossip
- Virtual Voting
These two methods work in simple ways.
Gossip about Gossip
Any node within a network needs to talk to each other. This is the premise of the Gossip over Gossip method. To get a clear picture, let’s take five nodes into account – Alpha, Beta, Gamma, Charlie, and Bravo. Each one of these nodes now starts a transaction — which leads to an “event” within the network.
During the event, each node calls the other two randomly designated nodes. These nodes are chosen randomly — to which the transaction details are shared. For example, Beta calls Gamma and Brave, whereas the Alpha node calls Charlie and Bravo. It is completely randomized, so we do not know which node will call the other. Once the event is over, all the nodes have called each other, creating a network where each node has the hash of the previous block. It is a tree-like system where you can visualize the leaves to be connected with other leaves. The way, each node connect with each other is what makes Hashgraph Technology so unique and amazing at the same time.
Virtual Voting
Virtual Voting works differently when compared to the “Gossip about Gossip.” Virtual Voting is used to reach a consensus for deciding the order of the transactions. Virtual Voting only starts when a certain amount of transactions are processed by nodes. For our example, let’s say that 15 events takes place before the virtual voting kicks in.
When the virtual Voting starts, each participant now looks for that particular event that fits into the network. It is known as a “famous witness.” In simple words, the chosen events contain information about the old events that are recorded by the nodes. If the new event fits with the old one, then it is voted as yes, otherwise, it is voted no. This way, an event gets the most votes and is now the “famous” witness for that “particular” round. The event then provides the transaction orders.
Hashgraph Whitepaper – Let’s get more technical
Now, that we have an eagle eye view of how a Hashgraph Technology works, it is time that we move on to its more technical aspects. We will go through its white paper and understand the key aspects below. You can check the white paper directly from here.
The purpose of going through the white paper is to get a better understanding of what Hashgraph has to offer.
In the white paper, the first thing that you will notice is how Hashgraph defines itself. It doesn’t call itself a fully-fledged system, and that’s true. It is basically a consensus algorithm or a data structure that offers a low-level building block rather than acting itself as a complete system. However, it does mention, “Hashgraph SDK” in a cryptocurrency system implementation.
Hashgraph opens up new ways we can solve complex problems. However, it the property of Swirls, Inc., and hence will never be open to the public. So, how it is going to be implemented to other projects — through partnership. They have already started their expansion, and one of those expansions include a collaboration with CULedger. CULedger will use the Hyperledger technology to build Credit Union’s distributed transaction processing solution. Clearly, we can see how the speed factor of Hyperledger is helping it to improve finance systems.
Want to know more about hyperledger technology? Enroll Now – Getting Started with Hyperledger Fabric
But, it is not entirely a closed ecosystem. Hashgraph offers an SDK library that makes it easy for anyone to experiment with its consensus library.
Programming language
The programming language used by the Hashgraph includes LISP and Java. The core is written in these two programming languages. However, it is inclined towards JVM language such as Scala, Java, etc. with the use of the SDK that the Hashgraph offers.
The open source community have been on the path to improve the Hashgraph offering, and hence have their own implementation in a different programming language. If you are interested, you can find the respective implementation below.
- Go https://github.com/mosaicnetworks/babble
- Python https://github.com/Lapin0t/py-swirld
- JavaScript https://github.com/buhrmi/hashgraph-js
Hashgraph technology is a great concept, and that’s why you will see it equally adopted in the open source community. It is fast, secure, and fair according to its white paper – or does it? Let’s look at Hashgraph technically.
How does it work? – A technical overview
Hashgraph consensus is a unique way to tackle the consensus problem. It utilizes Byzantine fault tolerance to replicate state machines. We can also see it as an “atomic broadcast” algorithm. This means that it establishes a link between the unordered transactions and order them accordingly. The process is ongoing, and the nodes can submit the transactions. Once done, each node then receives an ordered transaction output — containing all the submitted transaction. This way, all the nodes are connected, and each one has a copy of the “total order,” considering that each node has been ordered respective to the other nodes on the chain. It is an effective way of ordering transactions and connecting them together. This makes it ideal for the implementation of different cryptocurrencies, systems, and solutions.
Let’s look at the two functions.
submit_transaction(transaction) get_transaction(index) -> transaction or null
These two functions are at the core of how Hashgraph works. The transaction attribution in the submit_transaction function is an object that contains information such as fee, sender, receiver, amount, id, and so on. The information in the transaction object is used to identify its position within the network. The submit_transaction function is called by the node itself when it needs.
So, how does Hashgraph ensure that the transaction works as intended? It guarantees it by following the atomic broadcast algorithm.
- If a T1 transaction calls submit_transaction(T1) successfully, then the index in the calls of the get_transaction(index) should return T1 eventually.
- If get_transaction(index) call(any) returns T2 Transaction(not null), then it should return T2 or null for every call of get_transaction(index). It will eventually also return T2 for all calls.
The guarantee is important to ensure that every client in the Hashgraph sees the ordered output list using the same index(once the transaction is accepted by the Hashgraph.) The second guarantee, on the other hand, solves the double spending problem, which is crucial to ensure that no third-party malicious actor can harm the normal operation of the network.
Building a cryptocurrency using the Hashraph
Now that we have understood how the two functions work and ensure guarantee in a Hashgraph, we can use the knowledge to build a “basic cryptocurrency.” For now, we will only share the pseudocode that will cover the logic behind it.
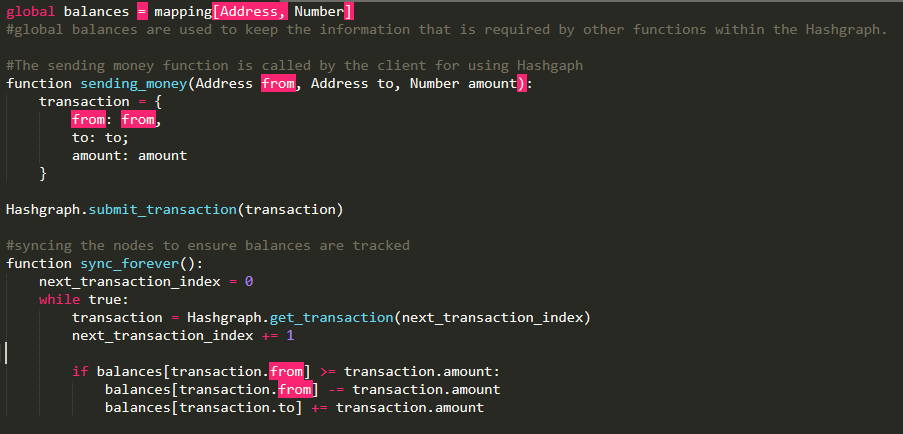
Pseudocode explanation
We need to declare a global array where the address and tracking numbers are stored. Now, the sending_money method is defined that is called whenever a node decided to use Hashgraph. It takes in three attributes, including the address of the receiver, sender, and the number amount as well. The amount is then stored in the transaction array.
In the sync_forever() function, we ensure that the transactions are in a loop. It also takes care of the nodes which exhaust their balance and is skipped as the balance returns a negative value. Each node is capable of seeing the same set of transactions in a particular order. This means once a transaction is updated, it is skipped by other nodes.
The above code is an example of how easy it is to create a cryptocurrency using Hashgraph. It is a basic cryptocurrency model, and you can always modify it according to your requirement. For example, you can add fees, add smart contract functionality, and so on. In short, Hashgraph can easily provide any cryptocurrency the required consensus to survive. Apart from that, the developer has to create other functionality required. This also means that the Hashgraph offers more flexibility compared to other similar solution.
The role of clients
In a network, the clients have to cover a lot of things. Each client is responsible for running the Hashgraph algorithm. This is similar to a fully decentralized blockchain where they have a copy of the ledger. Clients in Hashgraph also download the whole Hashgraph data structure and verify them using verification procedure. The verification procedure is done to check whether the transaction has been committed or not.
So, how does it differ from the nodes in a bitcoin network? The significant difference is the amount of data required by the clients to verify the transactions. In a bitcoin network, each node has to download the block headers and the proof for single transaction validation. Hashgraph, on the other hand, only requires a graph data structure. It’s a unique approach to ensure that it doesn’t need the whole data or a large amount of data to verify the transaction. In total, a client would require signature and events — which should amount to 128 bytes of data.
Understanding the Hashgraph algorithm deeply
Hashgraph offers an ideal solution for a system that is looking to provide a practical approach to solving consensus. The algorithm holds the key, and that’s why we will now go through the algorithm and understand how it works.
Let’s take a network with N number of nodes. For the consensus to be successful, it needs to make sure that it works even when there are malicious nodes in the network. Nodes can work together to lie for a transaction or delay packets knowingly. All of these means that there needs to be proper protection against these kinds of attacks or collaboration between nodes.
The Byzantine setting ensures that if any one of the requirements is met, two nodes can communicate effectively and ensure that the algorithm doesn’t fall apart.
Before we proceed further, let’s understand some terminology that is required to understand the algorithm.
- Directed acyclic graph(DAG): DAG is a data structure used in Hashgraph where each node connected to other nodes in a directed way, without cycles.
- Events: The events contains a set of transactions which are represented by the vertices in a Hashgraph. Each transaction consists of information including the event’s parents, node signature from where it is created and a timestamp.
- Timestamp: The timestamp is the real world time at which the event took place. Timestamps are considering that they impact the final ordering of the nodes.
- Collision resistant hash function: A collision-resistant hash function is used to ensure that all the information of an event is encoded correctly. It also ensures that the gossip history up to the event is certified and is not modified in any manner.
So, if an event takes place, it would be sent to the other nodes. The node that witnesses the new event will also know about the old event as it is verified using the consensus algorithm. It is all about localized analysis and making proper use of gossip events.
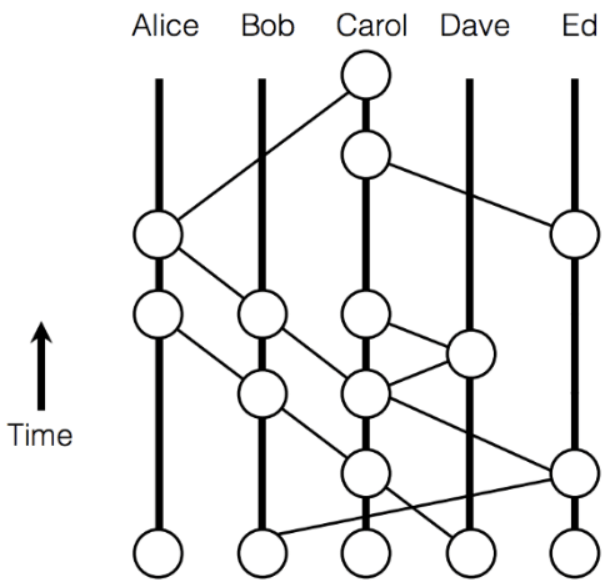
Image Source: Hashgraph whitepaper
In the above image, there are five nodes or clients, i.e., Alice, Bob, Carol, Dave, and Ed. Each of these nodes regularly connects (gossip) with, which gives rise to the events. When a node gossip, a new event with a valid signature and hash match is added to the graph. Only the events that are not seen before are added to the graph, which ensures no redundant information stays on the graph.
Once the sync is complete, any node that is receiving the event gets any transactions from the sending node and signs it off to create a new event. The process ensures that every new event has something new for the receiving node as the unique thing about the graph.
This way, the Hashgraph expand consistently with the help of the collision-resistant property. Every node that adds the event agrees to the past information, which makes Hashgraph its importance.
Want to build a career in enterprise blockchains, but not sure how? Enroll Now – How to Build Your Career in Enterprise Blockchains
Two key properties: Round Number and Binary Value
In the whole process, two key information is what makes Hashgraph possible. The first one is the round number, which is used in increasing order. The other key information is the binary value which determines if a client has witnessed an event or not. The value holds true for a particular round only.
The values are generated immediately when an event takes place. However, it is not as simple as it may sound. For example, the binary value can be any of the three: “undecided,” “definitely yes,” and “definitely no.” These three values are there considering that it takes a while to decide the value to be “definitely yes” or “definitely no.” When there is indecision, the value is set to “undecided.”
Three key features of Hashraph
Hashgraph has three key features that make it an excellent choice for different projects. In the white paper, it describes itself as secure, fair, and fast. To understand each of these features, let’s discuss them below.
-
Secure
The consensus algorithm does offer a secure way of handling transactions and ensure that an event is covered correctly. The order is what matters in Hashgraph, and the Hashgraph make sure that no malicious actor can fiddle with the data accuracy or the order in which the events are connected with each other. This way, it protects the network from both double spending problem as well as a 51% attack. It also effectively utilizes the resistant hash function and digital signatures. Once a transaction is committed, it cannot be reversed or changed. After all, it uses ABFT(Asynchronous Byzantine Fault Tolerant).
-
Fair
The fairness concept surrounds the idea of being fair to all the nodes in the network. It defines fairness by stating that an attacker will not be able to learn which two new transactions will make it to the consensus order. However, it is not clear how it can provide fairness to the Hashgraph. Apart from the white paper definition, the Hashgraph team also clarified through social media platforms that fairness works well if the majority of nodes know about the transaction. This can lead to a problem if an attacker gets hold of the 2/3rd of the participants. He can easily re-order the events without impacting on the fairness of the network. There is also no requirement of Hashgraph mining for the nodes.
-
Fast
Gossip methods are considered fairly fast. This is true in case of the Hashgraph’s gossip protocol. The events spread across the network fast considering that it is all about “gossip-about-gossip.” This also means that less information required to be propagated over time. Hashgraph also utilizes virtual voting, which makes it more efficient. But if we take into consideration that each node require entire Hashgraph, the size of the inbound should increase over time. For now, we do not know how it will impact the performance of the network. Theoretically, Hashgraph TPS can reach 5,00,000.
Want To Know More About Blockchain VS Hashgraph? Check Out Hashgraph VS Blockchain analysis Right Now!
Hedera Hashgraph
Until now, we have discussed the closed ecosystem of Hashgraph, its technical workings, and how it claims to be fast, secure, and fair. However, the biggest roadblock to the Hashgraph is its private nature. It is enterprise ready.
Meet Hedera Hashgraph, a Hashgraph network that is public and takes advantage of Hashgraph consensus algorithm. It takes full utilization of asynchronous Byzantine Fault-Tolerant Algorithm(aBFT). It offers guaranteed Byzantine fault-tolerance for replicated state machines.
Hedera Hashgraph establishes its idea on the top of Byzantine-Fault Tolerant(BFT) consensus(aBFT). The improved model will ensure that businesses can bring more value by using Hedera Hashgraph. It is also managed by the Hedera Hashgraph Council. The ultimate goal is to provide public access to Hashgraph capabilities and make the public utilize a secure and fast system for distributed ledger purposes.
Under the hood, both Hashgraph and the Hedera Hashgraph are similar. They both utilize the “gossip about gossip” protocol, which utilizes aBFT agreement to reach consensus. It also uses virtual voting, which means that there is no need for a central authority. It is entirely decentralized and offers a trustless environment for its uses.
The use of aBFT ensures fairness in all conditions — even when the network contains malicious actors. All the properties of Hashgraph are utilized within Hedera Hashgraph. However, to make sure that the Hedera Hashgraph is protected from DDoS attacks, the consensus algorithm doesn’t use the leader format.
With Hedera Hashgraph, you can build on trust. Some of the key applications of Hedera Hashgraph include cryptocurrency, smart contracts, and file services.
Services offered by Hedera Platform
With Hedera platform, you can enable some key services including the following:
- Cryptocurrency: Allows intermediates to use the network for cryptocurrency payments and let them take advantage of lower cost and simple design.
- Smart Contracts: You can also build smart contracts on top of the Hedera platform. To develop smart contracts, you need to use Solidity. As a developer, you can do atomic swaps, create assets, and deploy completely new applications.
- File Services: You can also use the Hedera platform to do file services, i.e., verify files. It is also a GDPR complaint.
Governance
The governance in the Hedera Hashgraph works differently. It can be divided into two tiers – The Governing Board and the Open Consensus.
The Governing Board is a centralized control system which is not an ideal solution for any network that wants to offer its services for the distributed ledger. The community is also not happy with its approach, and it is still one of the most significant criticisms of the Hedera Hashgraph.
The Open Consensus, on the other hand, is the consensus mechanism that we already discussed above. It governs how nodes can join and become part of the network, and also make it more decentralized. To ensure that there is a proper weighted voting model, it utilizes Proof-of-Stake. It ensures that collision is adequately mitigated, and there is also an appropriate incentive for users to run nodes.
Hedra Hashgraph Architecture
Hedra Hashgraph architecture is a three-layered architecture. It consists of the Internet Layer(Bottom), Hashgraph Consensus Layer(Middle), and Services Layer(Top). Let’s discuss each layer briefly.
- Internet Layer: The layer takes care of the communication between computers on the internet. It deploys TCP/IP connections with TLS encryption.
- Hashgraph Consensus Layer(Middle): The middle layer contains the nodes which participate in the network. These nodes take part in the consensus method using the Hashgraph consensus algorithm and gossip protocol.
- Services Layer: The topmost layer has their its own subgroups – File Storage, Cryptocurrency, and Hashgraph Smart Contracts.
The nodes earn the cryptocurrency for taking participating in the network. It is a native currency and ensures that the users get their incentive for participating.
The file storage, on the other hand, is Merkle-based. Moreover, if you are a developer, then you can also use Solidity as it is supported by the Hedra. Lastly, it offers smart contract support on the top of the network — giving you the ability to create scalable dApps.
Hedera Hashgraph dApps
There are few top Hedera Hashgraph dApps. They include Sagewise, Hearo.fm, Carbon, Cryptotask and Arbit.
Hedera Hashgraph Tools
There are many awesome Hashgraph tools out there. Few of the notable Hashgraph tools are as follows:
- Hedera Java SDK – SDK in Java for Hedera Hashgraph. It is maintained by Hedera LLC.
- Hedera Rust SDK – SDK in Rust, community-maintained
- Hedera Go SDK – SDK in Go, community-maintained
- Hedera Test – Test Hedera in action
- Hedera Java Keygen tool – A keygen tool used in Hedera Hashgraph for managing ED25519 key pairs. It is a command-line utility.
Hashgraph Communities
You can also engage with the Hashgraph communities and become part of their offering. To get started, check out Hedera communities on Telegram, Medium, and Twitter. If you are keen to talk with the Hedera Developer Chat, you can check the link here.
Conclusion
Hashgraph is an exciting concept that completely changes the playing field. It is comparatively faster than that of traditional distributed ledger technology, including blockchain. It is clearly a great implementation, but it’s close to nature can hinder its growth. Hedra Hashgraph, on the other hand, is a public Hashgraph network which makes proper use of Hashgraph. Also, there is no Hashgraph mining which makes the network more fair to everyone who is taking part in it.
*Disclaimer: The article should not be taken as, and is not intended to provide any investment advice. Claims made in this article do not constitute investment advice and should not be taken as such. 101 Blockchains shall not be responsible for any loss sustained by any person who relies on this article. Do your own research!